Catalyst Blog
Featured Post
SEARCH & FILTER
More From The Blog
Search for
Category
Understanding MLOps and DevOps
DevOps succeeds when implemented well because software delivery becomes an…
But Where Are You Going to Run All of Those Tests?
Something interesting is happening in QA teams right now. AI…
Fight Fire with Fire: Using AI to Fight AI
App attacks surged to 83% in January 2025, up from 65% just…
Virtual vs Real Devices: What Actually Matters in Mobile Testing
If you’ve spent any time testing mobile apps, you already…
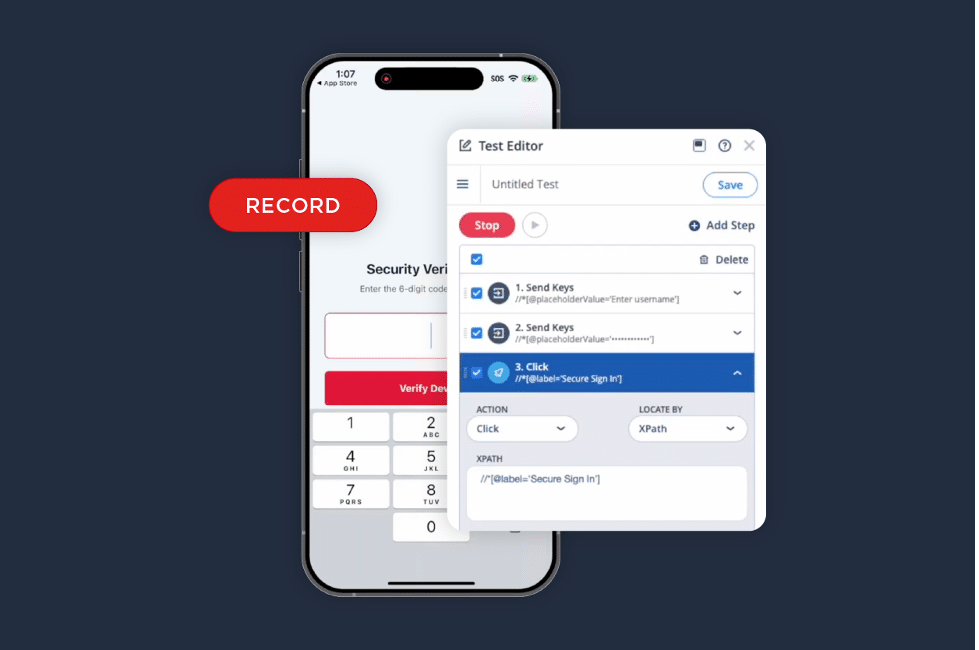
iOS Test Recorder: A Faster Way to Turn Validation into Automation
We listened to your feedback. The iOS Test Recorder is…
What Bad Guys 2 Taught Me About Information Asymmetry and the Application Security Problem Nobody Wants to Name
01 They Were Students of Your Work There is a…
Start Testing Samsung Galaxy S26 Series Today with Digital.ai Testing
Samsung has officially introduced the Galaxy S26 series, continuing its lineup…
Android 17 Beta Support Now Available with Digital.ai Testing
As we move closer to the anticipated release of Android 17 —…
Accelerating Test Creation using LLMs
Manual Testing Bottleneck Over the past couple of decades, software…