Catalyst Blog
Featured Post
SEARCH & FILTER
More From The Blog
Search for
Category
Native OKRs Inside Your Security Boundary: Strategy-to-Execution Without Another System
In many enterprises, strategy lives in one system, work is…
How Financial Teams Test Secure User Journeys Without Compromising Security
In financial applications, the parts that matter most—authentication, access control,…
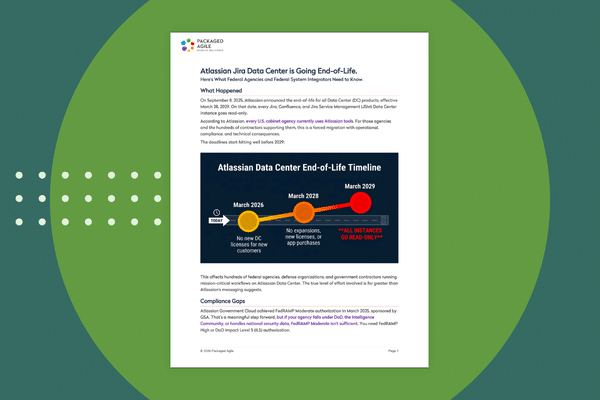
Ask Release: Leverage AI to Streamline DevOps
It’s 2:17 PM and a production release is stuck. Slack…
Why Most Financial Application Failures Aren’t Caught Before Release
A customer opens their banking app to transfer money. The…
What the Mainstream Press is Missing About Mythos
We’ve seen a few cybersecurity stories break into the mainstream…
Appium and Modern Mobile Frameworks: Understanding Automation Challenges
Mobile automation has matured significantly over the past decade, largely…
The Myth of Automation Lock-In: Migrating Quantum Without Rewrites
While talking with so many enterprise QA teams as a…
Automation First App Design Framework & Best Practices
A concept promoting how developers can design their apps to…
Agentic AI Attacks: Agent Smith is Out of Retirement
Nature-Free Evolution Attackers continue to push the bounds of AI…