Application Hardening for Mobile Payment Providers
Payment providers face relentless client-side attacks targeting the mobile applications that move money as well as the SDKs embedded downstream.
Digital.ai App Hardening protects both mobile payment apps and SDKs with layered, MPoC‑aligned defenses that preserve runtime integrity, safeguard cryptographic assets, and reduce fraud risk across every deployment.


Payment Ecosystem Risks

Partner Distribution Expands Attack Surface
Payment SDKs are distributed across partner and merchant apps, increasing risk in environments outside of your control.

End-user Apps Are Relentlessly Tampered With
Client-side apps run in hostile environments, where attackers can bypass controls or manipulate transactions at runtime.
Compliance Requirements Are Raising the Security Bar
EMVCo and PCI MPoC requirements demand stronger protections that actively resist tampering, analysis, and key extraction.
Secure Mobile Payments with Digital.ai
Protect SDKs Without Rework
Secure payment SDKs before distribution to app makers. Protect proprietary logic, embedded controls, and sensitive code paths without forcing development teams to rewrite applications or change release processes.

Harden Apps Post-build
Apply protections during the post-build process, so teams can secure payment apps late in the lifecycle. This reduces friction, preserves developer workflows, and helps speed deployment across mobile and other client-side environments.
Support EMVCo and MPoC Goals
Help payment providers align with EMVCo and MPoC expectations for application integrity, runtime protection, and resistance to tampering. Strengthen the security posture of payment apps operating on commercial off-the-shelf devices.

Defend Against Reverse Engineering
Obfuscation, anti-tamper, and anti-analysis protections make payment apps and SDKs harder to study, modify, and misuse. This helps prevent exposure of sensitive logic, transaction workflows, and implementation details that attackers or partners could exploit.
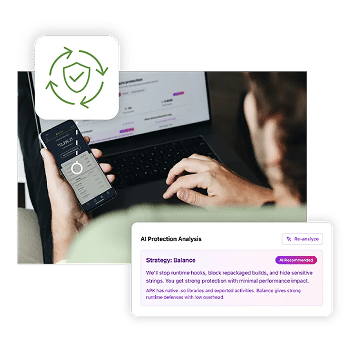
Monitor Threats in the Field
Runtime detection and threat telemetry provide visibility into attacks against protected payment apps. Security teams can see where protections are firing, understand attack patterns, and improve defenses based on real-world threat activity.

Book A Demo
Talk to a payments security expert.
Customer Success Story
Millions of Dollars
in cost savings
Improved Morale
among SOC staff

The successful defense of our customers’ mobile apps prevented the loss of thousands of customers.
Rodolfo Ramos
Information Security Executive Manager

Benefits for Payment Providers

Protect Payment SDK IP
Shield proprietary SDK logic from inspection, reuse, and unauthorized partner access.
Stop App Tampering
Prevent modification of payment apps that could bypass controls or alter transactions.

Resist Reverse Engineering
Obscure sensitive code and logic to slow analysis and frustrate attackers.
Support MPoC Requirements
Help meet MPoC expectations for app integrity and runtime protection.
See Attacks in Production
Detect live threats and gain insight into real-world attack activity.
Higher Customer Trust
Delivers safer mobile banking experiences that strengthen confidence and brand reputation.
We Are FIPS Validated
NIST FIPS 140-3 is the U.S. and Canadian government standard for validating the security of cryptographic modules. Certification confirms that encryption functions meet rigorous, independently tested requirements. For financial institutions, this validation provides assurance that protected data, keys, and cryptographic operations meet trusted, regulator-recognized security benchmarks.
FIPS 140-3 is technically harmonized with ISO/IEC 19790, which defines international security requirements for cryptographic modules. In other words, FIPS 140-3 is the U.S./Canada adoption of the same core standard that ISO/IEC 19790 specifies globally.