Published: April 17, 2026
What the Mainstream Press is Missing About Mythos
We’ve seen a few cybersecurity stories break into the mainstream press over the years: Kevin Mitnick as “uber hacker” in the ’90s, ILOVEYOU in the 2000s, Stuxnet in the 2010s, and Log4J at the start of the 2020s.
What is happening with Mythos is a similar inflection point. What the press has rightfully picked up on here and here and here and here is that Mythos has already found thousands of zero days, 99% of them are unpatched, some are decades old, and the vulns exist in every major OS and browser. If you haven’t read these articles, you should: The threat that Mythos and other LLM models pose is not hype.
In this post we’re going to dive into something the mainstream press is NOT covering: Mythos’s near-mythical ability to reverse engineer publicly available apps in the App and Play Store.
The Story Less Covered: What Mythos Means for App Resilience
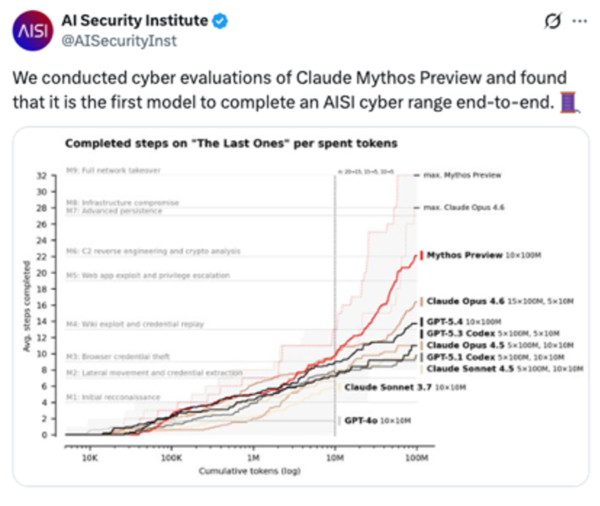
According to UK based govt funded AISI, Mythos can take a closed-source stripped binary, reconstruct plausible source code, and then find paths to back end servers even more easily and agentically than prior models could.
This is a different category than zero-day discovery. It reverses your app and turns it into a map (and a path) to your back-end systems.
We saw this coming, and we said so in “pre-Mythos” blog posts here and here. Mythos didn’t create this threat vector but it has effectively industrialized it. If Mythos can reconstruct source from a stripped binary, unobfuscated code is effectively open source to any sufficiently capable model. Leaving app code unobfuscated is like leaving Log4J vulns unpatched after the zero-day was disclosed. Roving models/agents are already downloading millions of binaries from the App and Play stores, reversing them, finding paths to exploit, and then merrily walking down those paths straight to your back end server.
“Table stakes” is now not *just* SAST, it is what OWASP calls “Resilience” to reverse engineering.
Mythos’s ability to reverse apps makes anti-tamper table stakes for apps in the same way SAST became table stakes as of ~2012. You cannot afford to not protect yourself against runtime analysis when runtime analysis can be done automatically and at the click of a button anytime and anywhere. It also makes protection against Static Analysis itself an imperative. If you are not obfuscating your code you are essentially open-sourcing your code, at least from the LLM’s perspective.
Fight Fire with Fire: Use AI to Configure Protections
The same AI accelerating attacks can accelerate defenses. We no longer have the luxury of spending a couple of weeks or months working with our customers to set up protection blueprints. Today Digital.ai uses LLMs to analyze the code we are protecting and to recommend and then write the protection blueprints themselves.
The Genie is out of the Bottle
There is no wishing Mythos back into the bottle, and no putting the toothpaste back in the tube. Anthropic estimates that models with comparable capabilities will reach broader availability within 12–18 months.
The good (well maybe not good but less bad) news is that the same forces accelerating the attack surface are available to defenders. Obfuscation that would have taken weeks to configure can now be designed, recommended, and written by the same class of models that threat actors are using to tear apps apart. The question is not whether to use AI in your protection strategy. The question is whether you get there before the adversary does.
Mythos didn’t change the rules of the game. It removed the grace period that let most teams play at their own pace. The teams that move now — obfuscating binaries, hardening against agentic RE, and using AI to configure protections at the speed of the threat — are the ones who will still have a defensible perimeter when equivalent models become generally available.
The rest will be facing the same fate that they faced when they were late to patch Log4J vulns, ignored nation-state-sponsored APTs, were slow to adopt AV after ILOVEYOU spread, and and ignored the power of social engineering after Kevin Mitnick was arrested.
You Might Also Like
What the Mainstream Press is Missing About Mythos
We’ve seen a few cybersecurity stories break into the mainstream…
Agentic AI Attacks: Agent Smith is Out of Retirement
Nature-Free Evolution Attackers continue to push the bounds of AI…
Fight Fire with Fire: Using AI to Fight AI
App attacks surged to 83% in January 2025, up from 65% just…



