Keys Are Exposed When They Are Hardcoded In Mobile & Desktop Apps
Building connected apps with innovative and responsive user experiences requires communicating and maintaining sensitive content.
Whether this content is a few bytes of data, feature updates, game scores, account information or video streams, it needs to be protected — no matter how or where it travels, rests, or is stored. Failing to protect content and communications with users can result in government penalties, fraud, and intellectual property theft — not to mention loss of customer trust, brand damage, and stolen revenue. Threat actors will exploit any and all app weaknesses in order to game fame, notoriety, government secrets or even just for the lolz.
Encrypting information throughout its lifecycle — in transit, at rest, and "in app" — is an important part of keeping sensitive data out of the wrong hands. Significant effort has been applied to securing data in transit, from secure transport layers to encrypting data from the source. The weak link in this chain is the endpoint: the app. The vulnerability of apps at endpoints, whether in mobile or desktop apps, had led to the growth of "Man-at-the-end" or MATE attacks.
Apps utilizing encrypted content use keys to decrypt incoming traffic and encrypt outgoing traffic — operations managed by functions inside the code of the application. If an app’s code is reverse engineered, the keys used to encrypt/decrypt content can be discovered and provide threat actors what they need to decipher encrypted information. Data resident in the app can be compromised along with all communications between the app and back office systems.
Challenges
- When an app is reverse engineered or its code is lifted, the keys used to encrypt/decrypt content can be discovered
- If cipher keys are uncovered, they can be copied, re-distributed, and used maliciously
- Once keys are copied, they can be used to observe data and communications with back-end servers
- Traditional data protection tools are not designed to defend keys from reverse engineered or otherwise compromised app code
If cipher keys are uncovered, they can be copied, re-distributed, and used maliciously. Detecting misuse of compromised keys is nearly impossible since they will be used through seemingly legitimate traffic. Once compromised, remediating a key breach is time and resource-intensive and requires re-keying and updating every app and process using those keys.
Traditional data protection tools were not designed to defend keys from being discovered via reverse engineering, code lifting, or otherwise comprising app code.
White-Box Cryptography ensures keys and data in mobile and desktop apps stay secure and thus protects communication between apps and back-end systems.
Digital.ai Key and Data Protection Product Brief
White-Box Cryptography ensures keys and data in mobile and desktop apps stay secure and thus protects communication between apps and back-end systems.
Digital.ai's Key and Data protection secures data in-transit by protecting the encryption/decryption keys stored within your mobile and desktop apps. Using mathematical techniques and transformations, Key and Data Protection uses white-box cryptography to blend (or *smear*) app code and keys to secure cryptographic operations, so that hardcoded keys cannot be found or extracted from the app to be used elsewhere.
Digital.ai's Key and Data Protection protects sensitive keys and data with a fully-featured white-box cryptography suite that protects mobile, desktop, and server apps. Key and Data Protection supports all major ciphers, modes, and key sizes, and can directly interoperate with other cryptographic packages (such as OpenSSL) and devices in your environment without requiring server-side changes.
We support symmetric encryption, Diffie-Hellman key exchange, hash-based message authentication codes, asymmetric encryption, signature generation, key wrapping & derivation, Shamir Secret Sharing, and "BigInteger" algebra.
In addition to supporting all major algorithms and modes, Digital.ai Key and Data Protection is the only white-box cryptography security product that is validated to meet FIPS 140-3 security requirements. Digital.ai White-Box Cryptography is available on iOS, Android, Windows, Mac, and Linux platforms.

Key Benefits
Prevent Encryption Keys From Being Extracted from Apps
White-box cryptography that manages, protects, and encrypts keys
- Combine app code and keys together for cryptographic operations
- Hide keys even when apps are reverse-engineered through dynamic instrumentation toolkits
Protect Communication between Applications and Back-End Servers
Protects encryption/decryption keys stored within an app
- Prevents key copying and redistribution
- Prevents "Man-in-the-middle" (MITM) and "Man-at-the-end" (MATE) attacks
Supports Various Platforms and All Major Ciphers, Modes, and Key Sizes
Protection of mobile, desktop, and server apps
- Fully-featured white-box cryptography suite that can be used for adding protection to mobile, desktop, and server apps
- Directly interoperates with other cryptographic packages (such as OpenSSL) and devices in your environment without requiring server-side changes
- Utilizes advanced techniques like Shamir Secret Sharing, Donna Curves, ECC, BigInteger Algebra, and Seeded XOR
Key Capabilities
Symmetric Encryption
- AES (128 or 256 bit, CBC, ECB, GCM)
- DES (Single, Triple)
Key Exchange
- ECC/DH (Diffie-Hellman)
- FCC/DH
Secure Hashing + HMAC
- SHA-1 / 2 / 3
- HMAC (SHA)
- CMAC (AES)
- DES MAC3
Asymmetric Encryption
- ECC/EG (ElGamal)
- RSA (2048, 3072, 4096 and larger key sizes)
Signature Generation
- ECC/DSA (Digital Signature Algorithm)
- RSA (2048, 3072, 4096 and larger key sizes)
Key Wrapping and Derivation
- NIST and CMLA Key Wrapping
- NIST, CMLA, and OMA Key Derivation
BigInteger Algebra
Provides means to perform modular arithmetic (addition and multiplication) in white-box form
Shamir Secret Sharing
Divides secrets that need to be encrypted into various unique parts
About Digital.ai
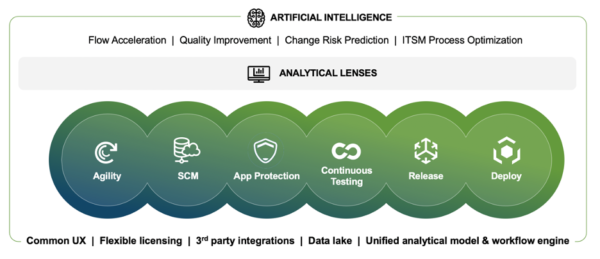
Digital.ai is an industry-leading technology company dedicated to helping Global 5000 enterprises achieve digital transformation goals. The company’s AI-powered DevSecOps platform unifies, secures, and generates predictive insights across the software lifecycle. Digital.ai empowers organizations to scale software development teams, continuously deliver software with greater quality and security while uncovering new market opportunities and enhancing business value through smarter software investments.
Additional information about Digital.ai can be found at digital.ai and on Twitter, LinkedIn and Facebook.
Learn more at Digital.ai Application Security