Connected vehicles are commonplace
Connected vehicles are now available from most manufacturers. Latest research estimates the global connected car market to increase 40% from 2016 to 2021. Great for consumers, but from a security perspective, this increase in connectivity represents a growing attack surface.
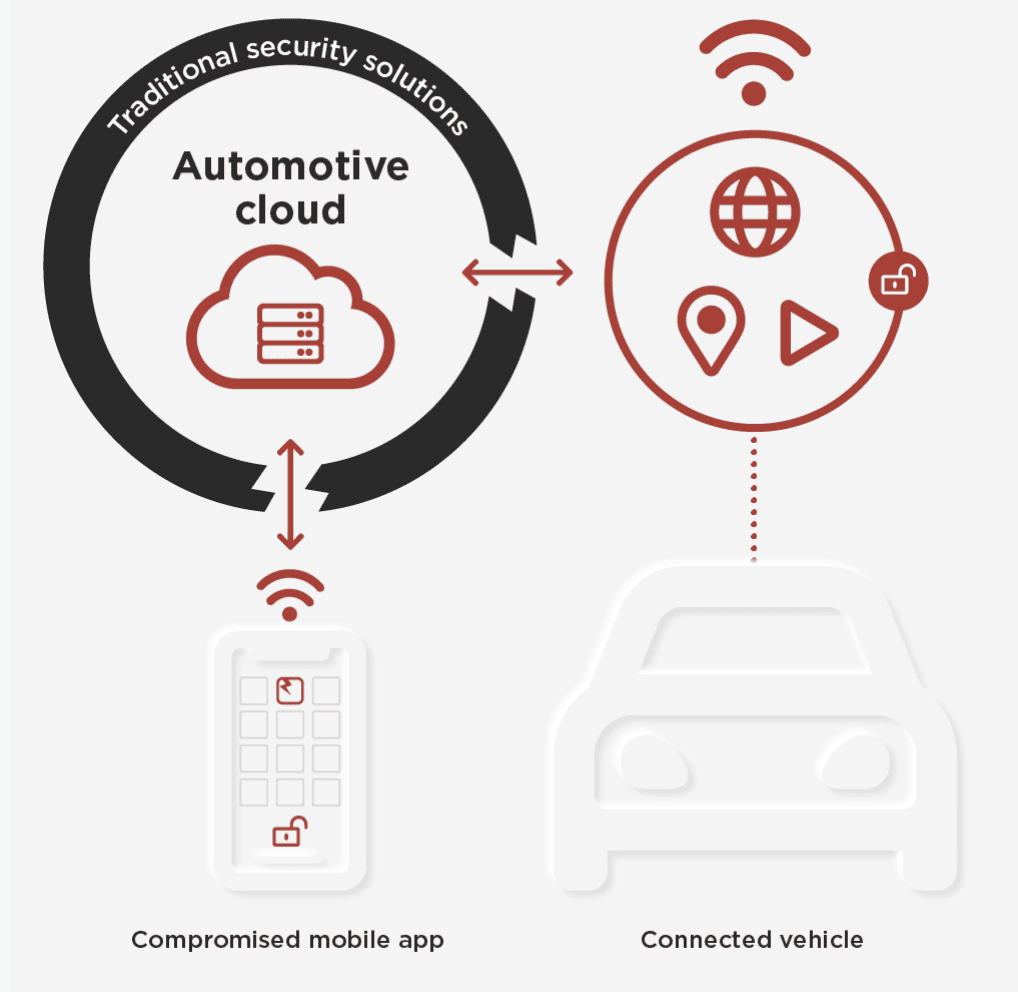
Utilizing an app to interact with a connected car is becoming as ubiquitous as a metal key. Unfortunately, this convenience comes at a price — apps downloaded from public app stores are easy targets for bad actors.
New threats require new solutions
While the industry’s Automotive Information Sharing and Analysis Center is developing best practices for connected car security, they do not prescribe specific technical or organizational solutions. Although a set of industry best practices is a good first step, these high-level guidelines aren’t requirements and take time to implement.
In order to address the serious threats facing today’s connected cars, auto makers and commercial car companies must reconsider their approach to app security.
Protecting a moving target
Connected car apps are equally vulnerable to attacks as any other app downloaded from a public app store. Without code protection, connected auto apps can easily be reverse engineered to steal code, intellectual property, personally identifiable information (PII), or give cybercriminals a way to communicate with back office systems. If the integration between a smartphone app and the Human-Machine Interface (HMI) of a connected vehicle is compromised, it can be used as a gateway to everything electronically tethered inside and outside the connected car.
Once an app is compromised, it can provide access to vehicle controls, including locks and ignition, voice recognition, dashboard buttons, navigation, and in extreme cases, computer-controlled throttles, steering, braking, and other autonomous vehicle operations. Breached applications yield control of external services such as infotainment, insurance, and banking accounts which can then be exploited for follow-on fraud.
Mobile app-level protection is critical
Attackers vary from lone wolves to nation states — all with varying motives, but they all share a few common traits: they are relentless, and they are ever evolving their attack methods. The potential for loss is high: business reputation, brand, financial loss, and most importantly, customer safety.
Coding best practices and traditional software protections cannot provide adequate protection against determined bad actors employing reverse engineering methods to attack apps. What is required to protect today’s connected automotive mobile apps is a layered approach that can secure app code from reverse engineering attacks and be applied during the DevSecOps process without interfering with build cycles. These layers should include:
- Obfuscation of code: Code obfuscation deliberately obscures app code, making it difficult for attackers to decipher and reverse-engineer
- Self-defense and integrity preservation: Automated defensive measures triggered by detected changes during runtime execution can invoke code self-repair or app functionality shutdown.
- Threat detection and the feedback loop: Detection and response are key to deterring app attacks. Real-time threat data can serve as an early warning of attacks in progress by notifying the business of compromised devices, attack methodologies, and attacker geolocations. Threat data can then be utilized in development feedback loops so app protection can be revised, and updated apps published as necessary to stop attacks.
Digital.ai Application Protection (formerly Arxan) solutions
Digital.ai Application Protection (formerly Arxan) solutions
Injects essential app code protections and threat detection sensors into CI/CD cycle after code development, without disrupting DevSecOps processes
Obfuscates source code, inserts honeypots, and implements other deceptive code patterns to deter and confuse threat actors
Triggers defensive measures automatically if suspicious activity is detected, including app shut down, user sandbox, or code self-repair
Notifies organizations of app reputation, real-time attacks, and provides the ability to suspend accounts or step up transaction or access authentication
Insights help optimize and adapt protection based on attack insights and trends including how, when, where, and by whom the app is targeted
Delivers threat data feeds end to end, making threat data accessible via a browser or easy integration with existing SIEM, BI, and fraud prevention platforms
Encrypts static or dynamic keys and data embedded or contained within app code
Protects sensitive data at rest within an app or in transit between the app and server
Supports all major cryptographic algorithms and modes with FIPS 140-2 certification
About Digital.ai
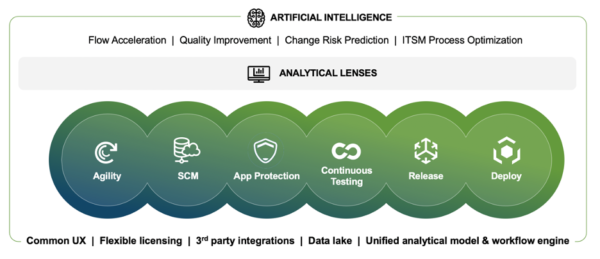
Digital.ai is an industry-leading technology company dedicated to helping Global 5000 enterprises achieve digital transformation goals. The company’s AI-powered DevSecOps platform unifies, secures, and generates predictive insights across the software lifecycle. Digital.ai empowers organizations to scale software development teams, continuously deliver software with greater quality and security while uncovering new market opportunities and enhancing business value through smarter software investments.
Additional information about Digital.ai can be found at digital.ai and on Twitter, LinkedIn and Facebook.
Learn more at Digital.ai Application Security